Privacy Risks in Data Collection and Storage:

There are many privacy risks in Data Collection and Strorage as technology keeps growing. One risk associated with collecting and storing personal information is that there is a high cost of data compliance, and it can cause the draining of a company’s money. The costs are higher due to the fact that companies need to meet with the standards of data privacy regimes, as well as the costs of drawing up security measures. Another risk associated with collecting and storing personal information is that due to the vast amount of user data, the companies will be responsible towards many people on how their data is used. Also, companies are sometimes asked to provide how their data is used, and they are forced to provide accurate information. Also, another privacy risk in data collection and storage is the risk of a data breach. A data breach can be used to maliciously use your personal information, which can lead to identity theft, blackmail, privacy violations, and they can steal your personal information. This risk can happen within the company or outside of it. It harms the company both ways, as they can be responsible for it, causing damage to the company’s reputation. Another privacy risk is hackers, as they are able to get into a company’s network and sell vast amounts of data. Companies are also liable to legal consequences if they cannot protect personal data. An example of someone stealing stored personal information is when an insider at Yahoo stole data to sell it to their competitors. He did this, so he could benefit financially. He stole and sold sensitive information of their strategy plans, and their analysis of The Trade Desk, their competitor. He would’ve been caught earlier on if they managed his activity better, as well as managed the USB devices being used. Organizations handle user data by using it to help with their targeted advertising, personalization for their website or product, and they can also sell it to third parties. Their usage of the data must be ethical. They can use cookies or other things to build data profiles, such as forms that the user fills out. This information can be used to positively affect the company with their marketing and money. They have to follow the compliance requirements when handling user data. They can also cut out and make some of the user’s information anonymous, to make sure no personal information or identities are leaked. Organizations can help handle potential security vulnerabilities by using technology, such as built in data protection and data loss prevention. Built in data protection can consist of encryptions, firewalls, and endpoint protection. They also use vulnerability assessments to help protect potential security vulnerabilities. They use network scans, web application scans, and host-based scans. This helps secure their collection of personal data and makes sure that it doesn’t get leaked.
Misuse and Protection of Computing Resources

Computing resources can be misused by having a lack of handling data properly, This can lead to the resources being stolen and misused. They can also have collection errors and improper filing, which can lead to the wrong information being collected, and it could cause a risk to the person’s information, as it could have been shared to the wrong person. Data misuse can also cause a data breach, which is an even bigger risk. Data misuse can happen for many reasons, such as for personal gain, carelessness, and to benefit the company. Data misuse can be used to help an employee start their own business, or someone can sell that information to third parties. Uneducated employees can sometimes mess up. They can download data to their own device, which is at risk of getting hacked, they can accidentally expose personal information, and they can share data with unauthorised people. All of these things can cause data to be misused. One case of when data was misused was when the Northern Ireland Police’s staff and workforce’s personal information was posted online. This was due to a data breach, caused by the carelessness of an employee. This caused people to be scared for their safety, it ruined the company's reputation, and it caused them to be fined a huge sum of money. Some strategies that protect systems and networks from exploitation are to verify the identity of every individual who has access to the system, which can be done by having a multi-factor authentication system. Another strategy to protect systems and networks from exploitation is to monitor logs and people’s activity on your system. This way you will have a clear list of what everyone is doing. You can also detect early signs of harmful activity by using this. You can also educate your staff and team, so they won’t accidentally leak the information or misuse it. Training them about the consequences of it will make them more careful and aware about it. Uneducated employees cause a huge chunk of data leaks and breaches, as they are too careless, causing them to make a mistake. Creating an insider threat policy can also help protect systems from exploitation, as it helps prevent misuse of data from employees. Another effective strategy is to set up alerts whenever an activity might have a potential threat. This can alert security, which can help get rid of inside exploitation. The alerts should cover all suspicious activity, which can make you act sooner on the matter. Automated alerts can make this much easier to manage. You can also assign properties to what a person has access to, so they are not able to do anything they aren’t supposed to.
Unauthorized Access to Information

Hackers and malicious actors gain unauthorized access by using softwares and code to take control of systems. They can also use these softwares to steal vast amounts of data. They use exploits to take advantage of the company’s bugs, giving them access to files, applications, and other resources. People also gain unauthorized access to information by guessing passwords and personal identification numbers. Researching and phishing are used to do this. Some hackers and malicious actors also use blackmail or other sorts of psychological manipulation to be able to get access. They can also impersonate staff and use links to be able to install viruses on their computer without them knowing. This way they can long into the computer and steal data. Phishing is another way hackers gain unauthorized access to information. They will send an email, which looks like it was sent by someone else, and they will attach an attachment to it. When individuals click on the email, the malware installs itself on the computer, giving the hacker unauthorized access to the information. Hackers and malicious actors can also gain unauthorized access to information from malicious staff. Staff can leak information to third parties or to malicious people. It can also happen accidentally, where staff will leak information. An example of this is when a staff member accidentally sends important and confidential information to the wrong person. Session hijacking can also cause people to get unauthorized access, as they are able to log in as a user, which gives them access to information. They do this by capturing the session id and they pose as a computer. This gives them access to the information, as web servers respond to their requests. A real world example of how hackers gained unauthorized access is when Microsoft was hacked, as they were able to gain unauthorized access from exploiting zero-day vulnerabilities. They were able to take over servers, request access for information, and were able to gain unauthorized access to many businesses.
Methods used for data breaches are phishing, ransomware, web applications, card skimmers, sql injection, etc. Phishing can be used for data breaches, as once they accept the form of contact, malware installs itself on the computer, giving the hacker data. Ransomware is another method for data breach, as once they get ahold of the files from other methods, they demand money to unlock them. Web applications and sql injections tie together. SQL injection is when code is placed into a website, corrupting it. Web applications also use vulnerabilities in the website’s code, which can give them access to a bunch of information from users on the website. This can give them certain information, such as addresses, credit card information, and other personal details. An example of this is when Adobe’s database was hacked. This caused them to pay 1.1 million dollars in legal fees, as they got 153 million records stolen. Credit card records, personal information, and passwords were all leaked. Some cybersecurity measures to prevent data breaches is to keep software up to date. This way they can’t exploit your website. Testing the vulnerabilities of your website and dataframe can help strengthen it, as you are able to find any known weaknesses or vulnerabilities. Multi Factor Authentication can also help with this, as well as encryption. This can prevent data breaches, as any credentials will not be enough to long in, and encryption can help make sure that the sensitive information is inaccessible for any threats. Educating staff can also help, as it will make sure no accidents will occur. Keeping track of who has access, and using real-time monitoring with automatic alerts can make sure that it is running smoothly. The alerts will also warn you if there is any suspicious activity happening. You can also monitor every device.
Benefits and Risks of Computing Innovations
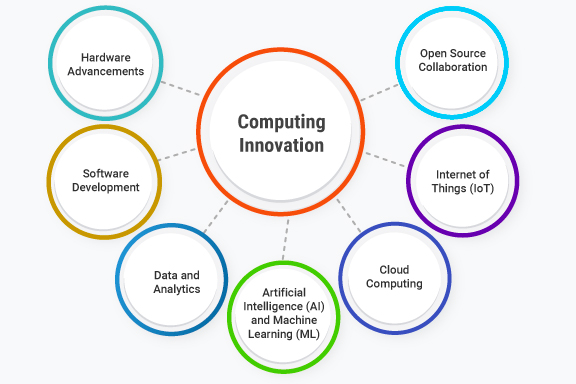
Computing innovations provide both benefits and challenges. An example of this is computing innovations in the medical field. Machines have helped save many lives, as there is new technology for medicine, CT scans, new and improved testing equipment, and safer operations. Medical images have also been advanced, as MRIs, and x-rays have become more accurate. New technologies have also been improved and added, such as artificial intelligence. Platforms to share information with millions of people and other social media platforms have shaped the current world. Communication has also been improved, as it has become faster and more reliable. Live chats, and calls have been updated, giving people the ability to talk face to face remotely. Multiplayer online video games have also brought communities of people together, and friends are able to bond through playing the game. Security has also been improved, giving people the ability to block out malicious people from accessing their data. Cameras that can be accessed from your phone are also a big help. Technology gives more access to information online, giving people the ability to explore their interests. Technology has improved our overall daily life from telling us the weather, having homework assignments online, having plenty of information accessible, and being able to watch online videos for entertainment. However, there are many challenges with the improvement of computing innovations. Some challenges of having computing innovations is the risk of getting hacked or your information stolen online. This can happen by malicious people either hacking websites you visit, which they can take your information from, or they can hack you. This gives a bigger risk of getting all of our information stolen, sold, or losing access to important files. The improvement of AI and other technologies are taking people’s jobs as well, leaving many unemployed. Less privacy is also a challenge, as websites can track your behavior. Being so dependent on technology is also a challenge, which can lower our health and can make us less dependent. Misinformation is also more accessible and visible online, giving people the wrong information. Another challenge of computing innovations is AI and technology not being 100 percent accurate. This is because online transactions can be misdirected, and there can be mistakes with your balance. Also there is technology, which is able to take all of your credit card information just by being near it. Technology has advanced crime, from the new tools that can be used. Cases where technological advancements have had unintended consequences beyond their original purpose have many examples. One of them being social media. Social media was meant to connect people across the world, however there is a lot of third-party abuse, political interference, and cyberbullying across the social media platforms. Social media can also mess with people’s mental health, as filters can make the norm look deceiving. It also has never been intended to have fake news spread on social media. The industrial revolution's purpose was to advance technology and increase productivity in factories. However, an unintended consequence beyond this purpose is air pollution. Some other technological advancements that have had unintended consequences is AI. AI was created to speed up processes and calculations, however now it has started to take people’s jobs. It also is being heavily used to plagiarize on writing assignments, print code for people to copy, and it creates a loss of privacy. A chunk of AI is being used for unethical purposes. Also, video games’ main purpose is to entertain people and be really accessible. However, this can cause people to gain weight and be unproductive, as they are glued to their screen. Also air conditioning has caused people to not sit on their porch outside to cool down. Now, due to the fact that most houses have AC, people do not use their porch, as they prefer to stay inside. This causes porches to not be needed, so newer homes are not built with porches. This causes people to not have a connection with their neighbors and activities become less social.
Sources
https://www.gls-startuplaw.com/blog/entry/what-are-the-risks-associated-with-collecting-personal-data
https://www.domo.com/learn/article/the-risks-of-collecting-and-storing-dark-data/
https://www.idx.us/knowledge-center/10-dangers-to-personal-information-infographic-available-is-your-informatio?form=MG0AV3/
https://usercentrics.com/knowledge-hub/data-is-the-new-gold-how-and-why-it-is-collected-and-sold/#:~:text=Companies%20want%20as%20much%20user,parties%20as%20a%20revenue%20stream/
https://cloudian.com/guides/data-protection/data-protection-and-privacy-7-ways-to-protect-user-data/#:~:text=By%20protecting%20data%2C%20companies%20can,%2C%20encryption%2C%20and%20endpoint%20protection/
https://www.cyberproof.com/vulnerability-management/vulnerability-assessments-key-steps-and-implementation/?form=MG0AV3/"
https://www.syteca.com/en/blog/real-life-examples-insider-threat-caused-breaches/
https://www.okta.com/blog/2020/06/data-misuse/
https://www.syteca.com/en/blog/4-ways-detect-and-prevent-misuse-data/
https://www.egnyte.com/guides/governance/unauthorized-access#:~:text=These%20vulnerability%20exploits%20are%20commonly,of%20systems%20and%20steal%20data.&text=Cybercriminals%20often%20gain%20unauthorized%20access,over%20credentials%20or%20sensitive%20data/
https://www.syteca.com/en/blog/detecting-and-responding-to-unauthorized-access#:~:text=Cyberattackers%20can%20exploit%20software%20flaws,websites%2C%20or%20attachments%20in%20emails/
https://www.rapid7.com/fundamentals/types-of-attacks/
https://www.upguard.com/blog/biggest-data-breaches-us/
https://corporatefinanceinstitute.com/resources/data-science/data-breach/
https://library.fiveable.me/ap-comp-sci-p/unit-5/beneficial-harmful-effects/study-guide/rErWKPcu55DLj7N7L8hZ/
https://www.forbes.com/councils/forbesbusinessdevelopmentcouncil/2019/06/07/five-benefits-and-three-challenges-technology-can-bring-to-global-companies/
https://cccblog.org/2024/05/20/4-ways-computing-can-positively-affect-society/